Neural Node 1800019900 operates as a distributed processing unit within an integrated lattice, coordinating through Cyber Pulse to thread real-time communications across neural modules. This discussion examines how the pulse shapes roles, interfaces, and constraints while foregrounding privacy, consent, and data governance as core primitives. Real-time threat anticipation, anomaly detection, and transparent telemetry are analyzed for governance, security, and accountability. The implications for cross-domain deployment raise practical questions that warrant careful, methodical consideration.
What Neural Node 1800019900 Cyber Pulse Is All About
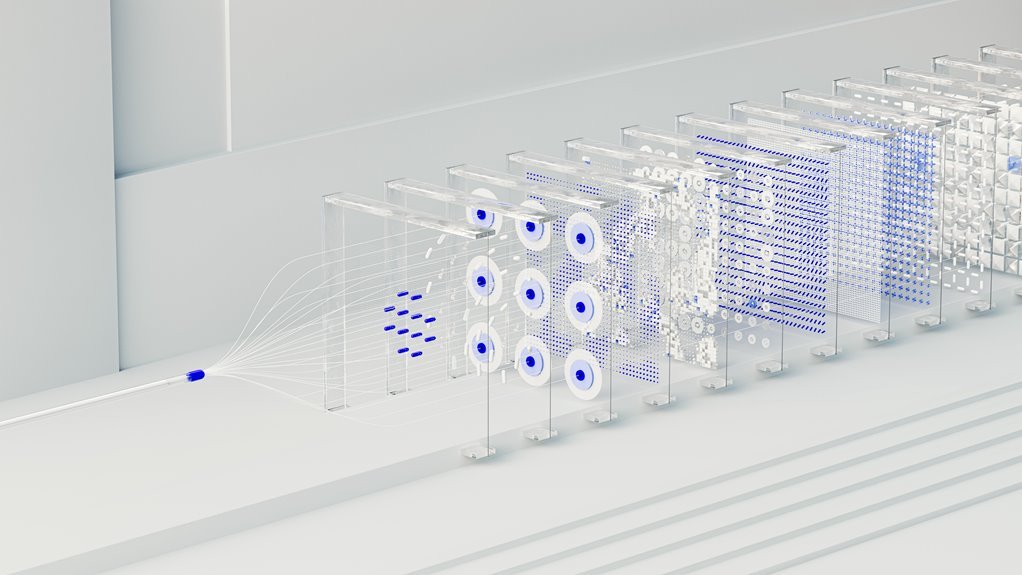
The Neural Node 1800019900 Cyber Pulse represents a conceptual framework for examining how advanced neural modules coordinate to process high-velocity data streams. It outlines roles, interfaces, and constraints that shape system behavior.
A neural node functions as a processing unit within a distributed lattice, while cyber pulse describes synchronized signaling. Privacy concerns and data governance emerge as essential design primitives.
How the Cyber Pulse Anticipates and Detects Threats in Real Time
How does the Cyber Pulse anticipate and detect threats in real time? The system integrates continuous monitoring, anomaly profiling, and rapid correlation across endpoints, networks, and clouds. It quantifies threat latency, measures signal-to-noise, and triggers automated containment. Transparent telemetry supports data sovereignty, enabling localized decision rules while preserving global visibility for proactive defense and precise incident classification.
Ethical, Privacy, and Accountability Considerations for This Tech
Ethical, privacy, and accountability considerations for Neural Node 1800019900 Cyber Pulse center on balancing proactive defense with individual rights and governance.
The analysis identifies privacy concerns as central to trust, demanding transparent data handling, minimization, and consent.
Accountability frameworks delineate responsibility across operators and developers, enabling audits, explainability, and corrective action to ensure secure, lawful deployment without compromising personal freedoms or civil liberties.
Practical Implications for Industries: Use Cases and Best Practices
In industry deployments, Neural Node 1800019900 Cyber Pulse enables proactive threat detection, rapid incident response, and continuous posture improvement across operational environments by integrating telemetry, analytics, and automated controls with human oversight.
The use cases reveal scalable, cross-domain applicability, while best practices emphasize governance, transparent auditing, and risk-based prioritization to sustain robust security without compromising operational freedom.
Conclusion
A silvery lattice hums, threads of Cyber Pulse weaving through neural nodes like dawn-lit spiderwebs. Each beat maps risk, each echo reveals anomaly, a measured cadence of vigilance. The system stands as a transparent loom—data flowing with consent, governance inked in auditable trails. In this careful choreography, defense is proactive, ethical guardrails are visible, and cross-domain scalability unfolds like a lucid, well-charted shoreline—predictable, resilient, and poised for responsible deployment.